Latest Post
Using cURL for basic web…..exploitation
Applications like the browsers we use every day to access...
Read MoreR&E #03: Gathering System Information (Host Enumeration)
Today’s post will be about...
Read MoreLinux 101 #03: Linux Workflow (Cont)
A file descriptor (FD) in...
Read MoreLinux 101 #02: Linux Workflow
Let us start with the...
Read MoreTHM [Easy Lab] – Creative
Exploit a vulnerable web application and some misconfigurations to gain...
Read MoreCPTS #10: Windows Privilege Escalation
We have determined that this website has a command injection...
Read MoreTHM [Easy Lab] – Hacker vs. Hacker
Someone has compromised this server already! Can you get in...
Read MoreHTB – API Attacks – Skills Assessment
According to the challenge description, the Inlanefreight E-Commerce Marketplace company...
Read MoreAFK #01: Dragon Symphony – Zyusouken
The first post in the “Away From Keyboard” section. Aside...
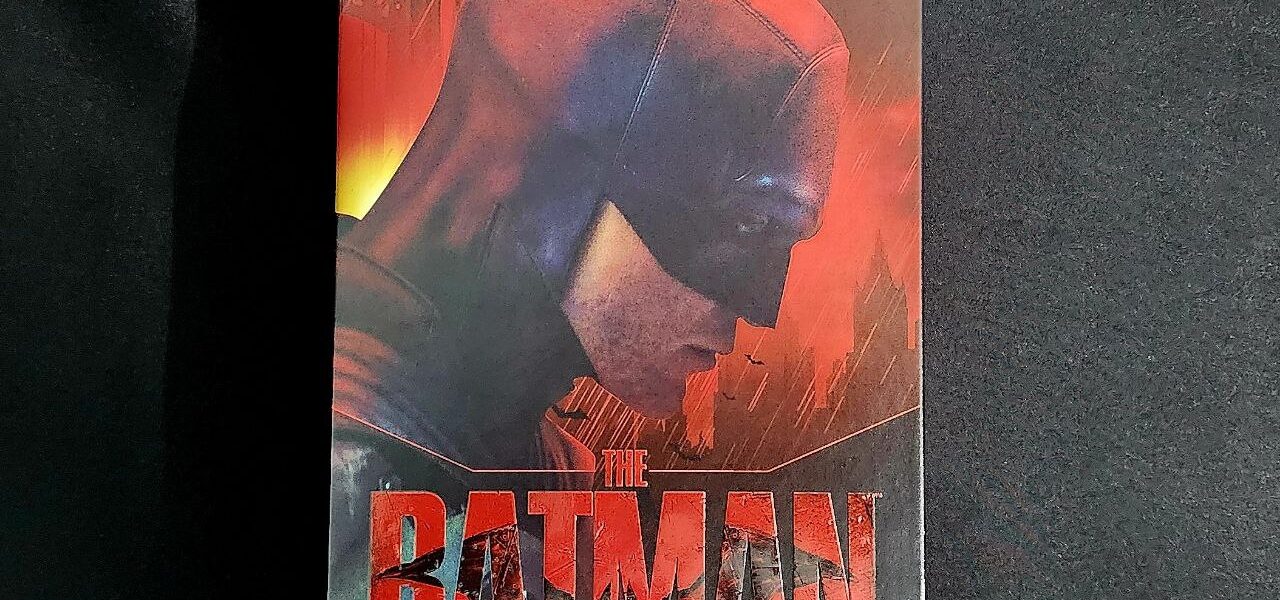
Read MoreAFK #03: Fondjoy The Batman 2022
Once again, I’m back with another Fondjoy figure. (Hmm, I’ve...
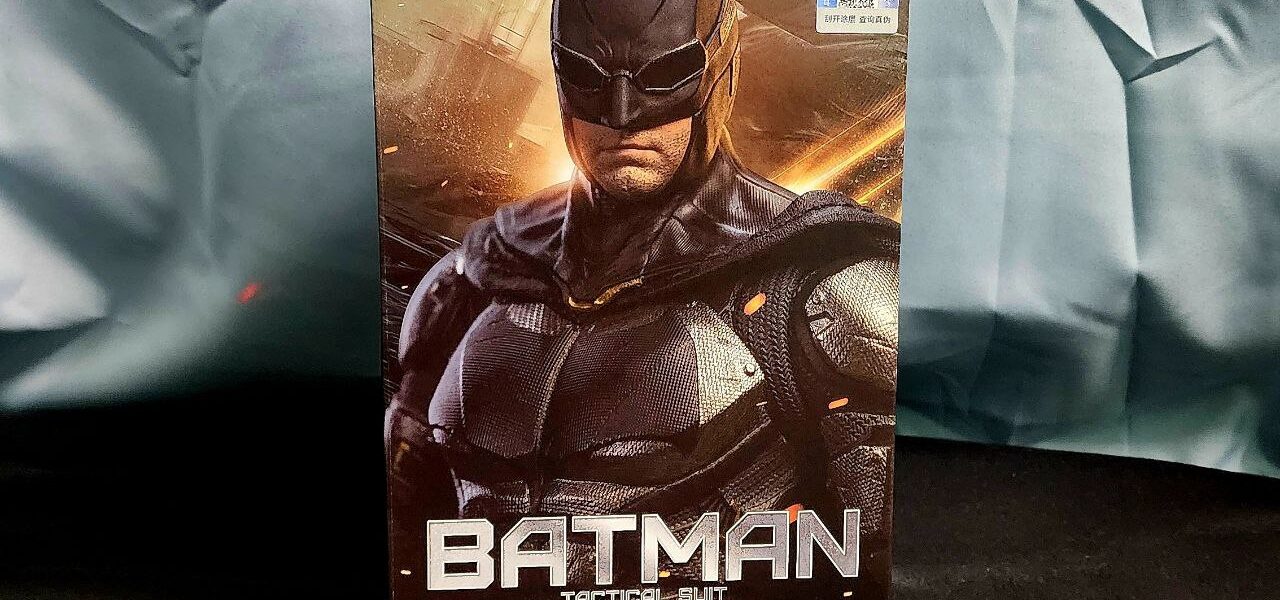
Read MoreAFK #02: Fondjoy Batman Tactical Suit
This is the first Batman figure I’ve ever purchased. So,...
Read More